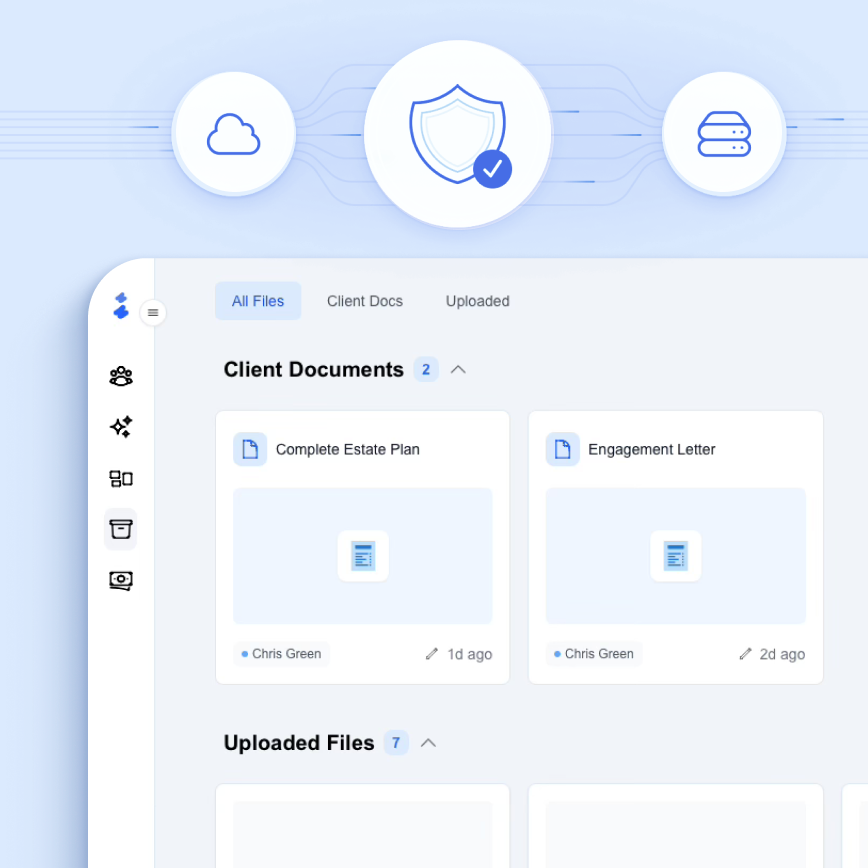
Enterprise-Grade Security
Your data security is our top priority. We implement comprehensive security measures and follow industry best practices to protect your sensitive information.
OVERVIEW
Industry-Leading Data Security
Our security practices are informed by leading industry certifications
Comprehensive Encryption
From front-end traffic (SSL/TLS) to data at rest (AES-256), encryption is consistently applied throughout our architecture.
Strict Access Controls
Role-based vector store permissions, secure database credentials, and environment variable encryption limit unauthorized access.
Audited & Compliant
Relaw's infrastructure providers are SOC 2 Type II certified, meaning they undergo regular third-party audits of their security practices.
SECURITY FEATURES
Comprehensive Protection
Multi-layered security measures to protect your sensitive data
Hosting & Deployment
SOC 2 Type II certified infrastructure with comprehensive DDoS protection
- SOC 2 Type II compliance with regular audits
- GDPR & CCPA compliance ready
- Data encryption at rest and in transit
- DDoS protection and monitoring
- Isolated deployment environments
Database Security
Multi-layered database protection with industry-standard encryption
- AES-256 encryption at rest
- TLS encryption in transit
- Role-based access control (RBAC)
- Network isolation
- AWS infrastructure compliance
Messaging & Queuing
Secure message delivery with token-based authentication
- TLS encryption for all endpoints
- Token-based authentication
- Message signature verification
- High availability design
- Secure message delivery
Transport Security
End-to-end encryption with SSL/TLS for all user connections
- HTTPS encryption
- Data confidentiality
- Integrity protection
- Secure user connections
- Browser security indicators
Ready to secure your practice?
Join forward-thinking law firms who trust Relaw to protect their sensitive data with enterprise-grade security.
QUESTIONS?
Get in Touch
Have questions about our security measures? We're here to help.